Banking malware in Google Play targeting many new apps
01 April 2017
Jump to
Introduction
While casually browsing my daily notifications on Koodous I found banking malware on Google Play, which has many new banking app targets in its configuration. A new sample was flagged by one of my BankBot rules: Funny Videos 2017. It struck me as different than the usual BankBot samples since it was tagged as using DexProtector, a tool to heavily obfuscate APKs. In addition the app name wasn’t the usual popular name (i.e. Flash Player, HD Coded or Google Play Update), so I figured I’d check it out a bit more.
Looking at the names of the activities and other manifest items it seemed like a normal app with inserted malware. I had read about another sample of the malware recently that was inserted into an existing app and uploaded to Google Play, so I figured I would check Google Play just to be sure. Still to my surprise it was actually there in Google Play.
Figure 1: Funny Videos 2017 app in Google Play (update: no longer available)
Apparently the app was updated recently (April 8, 2017) and this was most likely when the malware was added. I reported the app through their reporting system but at the time of writing it is still available in Google Play. As you can see it does appear to have 1k to 5k installs, which isn’t much for a normal app, but quite a lot for malware (at least compared to the installation counts we’ve seen so far on other mobile banking malware).
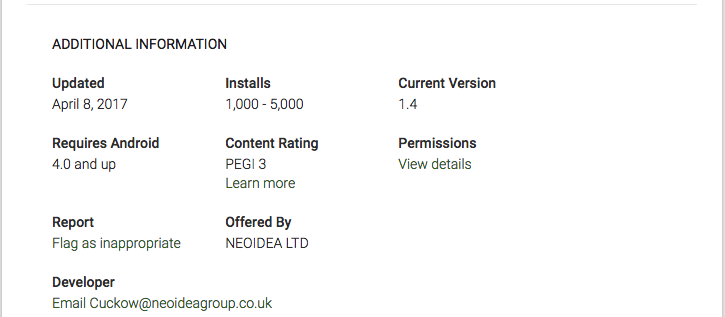
Figure 2: additional Google Play app info
Details
It is known that this technique has been used before, but is there anything interesting about this sample besides that it is available in Google Play? One of my co-workers was eager to look into it so he decided to run it on a device and captured some traffic:
HTTP/1.1 200 OK Server: nginx Date: Wed, 12 Apr 2017 20:01:45 GMT Content-Type: text/html; charset=utf-8 Connection: close X-Powered-By: PHP/5.4.16 Content-Length: 40513
<tag>yy kkk kmy or kme yg kko yg kkm kkr kmt or yy kmk kkl kkt kkg yh kmk kkt kmt eg tm gm yy kkk kmy or kme yg kko yg kkm kkr kmt or yy kmk kkl yh yg kkm kmg eg tm gm yy kkk kmy or kkl kkk kll kmt kkr kko kkk kkm or kmt kkt yy kmk kkl eg tm gm yy kkk kmy or kkt kkk kml kkr kkr kmk yy kmo or kmt kkt yh yg kkm kmg yg kkt kmt eg tm gm yy kkk kmy or kkr kmk yh eg tm gm yy kkk kmy or yg kmg yh yg kkm kmg or yg kkm kmm kko kkk kmt kmm or yg kkl kkl kkt or yg kmg yh yg kkm kmg yt kmm kmt kko kmk kmg kkr eg tm gm yy kkk kmy or yg kmg yh yg kkm kmg or kkt kkk kml kkr kkk kkr kkl eg tm gm yy kkk kmy or yg kmg yh yg kkm kmg or yg kkm kmm kko kkk kmt kmm or yg kkl kkl kkt or yg kmg yh yg kkm kmg yt kmm kmt kko kmk kmg kkr yt kkr yg yh kmh kmk kkr eg tm gm yy kkk kmy or klk kmg yh or yg kkm kmm kko kkk kmt kmm kkr yg yh kmh [removed for brevity] kkk kko kme or kmy kmt yy kko kkk kmk kmy kkg or yg kkm kmm kko kkk kmt kmm or kmy kkk kmm kmk kmh or yy kkk kmy kmy kkk kkm or hr ho ht kkt kmk kko rt kkl kkl kmh kmt yy yg kkr kmt kkk kkm gr ge gh g eg tm gm yy kkk kmy or kme kkk kkk kme kmh kmk or yg kkm kmm kko kkk kmt kmm or oy kme kmy oy eg tm gm yy kkk kmy or kkl yg klk kkl yg kmh or yg kkm kmm kko kkk kmt kmm or kkl tm kkl kmy kkk yh kmt kmh kmk eg tm gm yy kkk kmy or kkl yg klk kkl yg kmh or kmo kmk kko kmk eg tm gm kkm kmk kkr or yg kkr kkk kkt or yg kmh kko yg kmr kmo kmt or kmy kkk yh kmt kmh kmk kmg kky eg tm gm kmk kkt or kmh yg yy yg kmt klm yg or kmo yy kmk kmt yy kkk kkm tm eg tm gm yy kkk kmy or klk kmg yh or yg kkm kmm kko kkk kmt kmm eg tm gm 1yy kkk kmy or yg kkm kmm kko kkk kmt kmm or kkh kmk kkm kmm kmt kkm kme1 eg tm gm </tag>
Looking at the data that came from the server I immediately noticed the ‘<tag>[obfuscated data]</tag>’ format that I had run into earlier so I started searching for the code to deobfuscate it. Since the DexProtector obfuscated APK takes some time to deobfuscate and most malware doesn’t update very quickly I decided to get a recent BankBot sample that wasn’t obfuscated this heavily to obtain the deobfuscation routine. I ended up using sample 7c2e913571dad579fc8fa3a03171cf523e86a0686e1ba14f277da33569410646 for this purpose since it’s very recent (March 28, 2017) and also had the ‘/private/inj_lst.php’ request URL inside it. I cleaned up the deobfuscation routine from the sample a bit and ended up with the following code:
import java.net.URLDecoder;
public class Deobfuscator {
public static String deobfuscate(String obfuscatedText) { int j = 0; String result = “”; String key = “mkleotrghyua”; int i = 0; try { while(i < key.length()) { obfuscatedText = obfuscatedText.replace(key.substring(i, i + 1), “” + i); ++i; }
String[] strArr = obfuscatedText.split(“ “); while(j < strArr.length) { result = result + (((char)Integer.parseInt(strArr[j]))); ++j; } } catch(Exception e) { } return URLDecoder.decode(result + “ “); }
public static void main(String[] args) { String obfuscated = “”; System.out.println(Deobfuscator.deobfuscate(obfuscated)); } }
The key in the sample used for comparison ended up being the same as used in the Google Play sample, so I was lucky enough not to have to spend any additional time figuring that out. Throwing the obtained server data into the Java code and running the program resulting in the deobfuscated data containing a list of all apps that are targeted.
To our surprise the list was more extensive than expected and for the first time contained some new Dutch targets including ABN, Rabobank, ASN, Regiobank, and Binck. The full list can be found below. After seeing one of our customers on the target list we decided to update our detection signatures so we can now also detect this sample in our effort to prevent online banking fraud. I guess the game has started once again after some nice and quiet period. So far I have no reason to believe the functionality of the malware is significantly different from the previous samples, but I’ll have a closer look at it.
Update
Google has decided to take the app out of the Play Store. As it turns out, the malware is mostly phishing for credit card details and internet banking credentials. Screenshots of some of the phishing overlays can be seen in the image below.
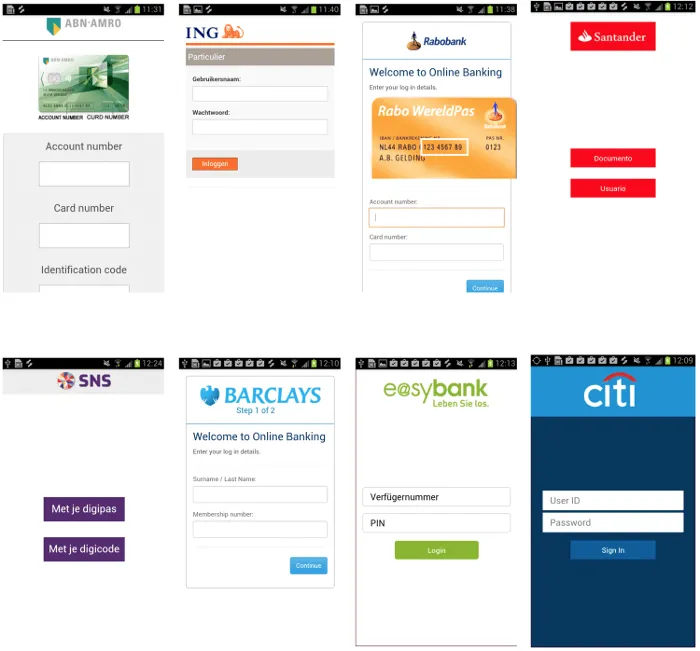
Figure 3: collection of overlays
Targeted apps
aib.ibank.android aib.ibank.android.tablet ar.bapro ar.bapro.tablet ar.com.redlink.ciudad ar.com.santander.rio.mbanking ar.macro ar.nbad.emobile.android.mobilebank at.bawag.mbanking at.bawag.tablet at.easybank.mbanking at.erstebank.george at.ing.diba.client.onlinebanking at.oberbank.mbanking at.psa.app.bawag at.spardat.netbanking at.volksbank.volksbankmobile au.com.amp.myportfolio.android au.com.bankwest.mobile au.com.heritage.app au.com.ingdirect.android au.com.macquarie.banking au.com.mebank.banking au.com.nab.mobile au.com.nab.mobile.android.nabconnect au.com.pnbank.android au.com.suncorp.SuncorpBank biz.mobinex.android.apps.cep_sifrematik cedacri.mobile.bank.asti cedacri.mobile.bank.bppb cedacri.mobile.bank.desio.brianza ch.raiffeisen.android ch.raiffeisen.phototan co.uk.Nationwide.Mobile com.AlinmaSoftToken com.BOQSecure com.BankAlBilad com.CredemMobile com.EurobankEFG com.IngDirectAndroid com.QIIB com.SifrebazCep com.VBSmartPhoneApp com.a2a.android.burgan com.abnamro.grip com.abnamro.nl.mobile.payments com.abnamro.nl.mobile.wallet com.adcb.bank com.adib.mbs com.akbank.android.apps.akbank_direkt com.akbank.android.apps.akbank_direkt_tablet com.akbank.softotp com.alahli.mobile.android com.alinma.smartphone com.alpha.pass com.amanalrajhi com.anz.android.gomoney com.appfactory.tmb com.arabbank.arabimobile com.axabanque.fr com.axis.cbk com.bancamarch.bancamovil com.bancomer.mbanking com.bancsabadell.wallet com.bankaustria.android.olb com.bankia.wallet com.bankinter.launcher com.bankinter.portugal.bmb com.bankofireland.mobilebanking com.bankofqueensland.boq com.bankofqueensland.boqtablet com.barclays.android.barclaysmobilebanking com.barclays.bca com.barclays.portugal.ui com.bawagpsk.securityapp com.bbva.bbvacontigo com.bbva.bbvawalletmx com.bbva.netcash com.bbva.netcashar com.bbva.nxt_tablet com.bendigobank.mobile com.binckbank.evolution com.bnpp.easybanking com.boi.tablet365 com.boubyanapp.boubyan.bank com.boursorama.android.clients com.bsffm com.business_token com.caisse.epargne.android.tablette com.caisseepargne.android.mobilebanking com.cajamar.GCCajamar com.cajasur.android com.carrefour.bank com.cba.android.netbank com.cba.shiraz com.cbd.mobile com.cbq.CBMobile com.cic_prod.bad com.cic_prod_tablet.bad com.citi.regional.argentina com.citibank.mobile.au com.citibank.mobile.citiuaePAT com.cleverlance.csas.servis24 com.cm_prod.bad com.cm_prod_tablet.bad com.comarch.mobile com.comarch.mobile.banking.bnpparibas com.comarch.security.mobilebanking com.comdirect.phototan com.commbank.netbank com.commerzbank.kontostand com.commerzbank.photoTAN com.cs.vasco com.csg.cs.dnmb com.db.mm.deutschebank com.db.mobilebanking com.db.pbc.miabanca com.db.pbc.mibanco com.db.pbc.phototan.db com.db.tabbanking com.defencebank.locationapp com.dib.app com.ducont.meethaq com.ducont.muscatbank com.entersekt.authapp.dkb com.ezmcom.softtoken.adcb com.finansbank.mobile.cepsube com.finanteq.finance.ca com.firstdirect.bankingonthego com.fpe.comptenickel com.fullsix.android.labanquepostale.accountaccess com.fusion.banking com.fusion.beyondbank com.garanti.bonusapp com.garanti.cepbank com.garanti.cepsubesi com.getingroup.mobilebanking com.gieseckedevrient.android.wallet.rabo com.google.android.1gm1 com.greater.Greater com.grppl.android.shell.BOS com.grppl.android.shell.CMBlloydsTSB73 com.grppl.android.shell.halifax com.hipotecario.mobile com.hsbc.hsbcukcmb com.htsu.hsbcpersonalbanking com.icbc.mobile.abroadARG com.icomvision.bsc.mobilebank com.ideaknow.ing com.ie.capitalone.uk com.iflex.fcat.mobile.android com.imb.banking2 com.ing.diba.mbbr2 com.ing.diba.smartsecure2 com.ing.mobile com.ing.mobilepayments com.ingbanktr.cuzdan com.ingbanktr.ingmobil com.intertech.mobilemoneytransfer.activity com.isis_papyrus.raiffeisen_pay_eyewdg com.kbc.mobilebanking com.kfh.kfhonline com.kutxabank.android com.kutxabank.appatxas com.kuveytturk.mobil com.latuabanca_tabperandroid com.latuabancaperandroid com.latuabancaperandroid.ispb com.latuabancaperandroid.pg com.lcl.application.tablette com.lloydsbank.businessmobile com.magiclick.odeabank com.mbanking.nbb com.mediaengine.allianzbank com.mediolanum.android.bst com.mediolanum.android.fullbanca com.mediolanum.android.wallet com.mobileloft.alpha.droid com.mobilenik.bsf com.mobilenik.ubika.bna com.monitise.client.android.clydesdale com.monitise.client.android.yorkshire com.monitise.coop com.mosync.app_Banco_Galicia com.nbo.ar com.nbo.mobs com.ncb.softtoken com.nearform.ptsb com.niobiumlabs.eurobank.activity com.ofss.fcdb.mobile.android.phone.bahl.launcher com.opentecheng.android.webank com.paypal.android.p2pmobile com.paypal.here com.posteitaliane.postemobilestore com.pozitron.anb com.pozitron.ingkurumsal com.pozitron.iscep com.pozitron.vakifbank com.rak com.rbs.mobile.android.natwest com.rbs.mobile.android.natwestbandc com.rbs.mobile.android.rbsbandc com.rbs.mobile.android.rbsm com.rbs.mobile.android.ubn com.rev.mobilebanking.westpac com.rsi com.rsi.ruralviatablet com.s4m com.sa.baj.aljazirasmart com.sabb com.samba.mb com.scb.ae.bmw com.scrignosa com.sella.BancaSella com.softtech.isbankasi com.solidpass.main.bsf com.starfinanz.mobile.android.dkbpushtan com.starfinanz.mobile.android.pushtan com.starfinanz.smob.android.sbanking com.starfinanz.smob.android.sbanking.tablet com.starfinanz.smob.android.sfinanzstatus com.starfinanz.smob.android.sfinanzstatus.tablet com.supervielle.mBanking com.swmind.vcc.android.bzwbk_mobile.app com.targo_prod.bad com.targo_prod_tablet.bad com.teb com.tecnocom.cajalaboral com.tescobank.mobile com.tmob.denizbank com.tmobtech.halkbank com.ubank.internetbanking com.ubs.swidK2Y.android com.ubs.swidKXJ.android com.unicajaTabletas com.unicredit com.vakifbank.mobile com.vipera.ts.starter.FGB com.vipera.ts.starter.MashreqAE com.vipera.ts.starter.MashreqQA com.vipera.ts.starter.QNB com.ykb.android com.ykb.android.db com.ykb.android.mobilonay com.ykb.androidtablet com.ykb.avm com.zentity.ing com.ziraat.ziraatmobil coop.bancocredicoop.bancamobile cz.airbank.android cz.csas.app.mujstav cz.csas.business24 cz.csob.smartbanking cz.csob.smartklic cz.kb.mba.business cz.mbank cz.moneta.smartbanka cz.rb.app.smartphonebanking cz.sberbankcz cz.ulikeit.fio de.adesso.mobile.android.gadfints de.comdirect de.comdirect.android de.commerzbanking.mobil de.consorsbank de.dkb.portalapp de.dzbank.kartenregie de.fgi.ms.securesign de.fgi.ms.vrsecurecard de.fiducia.smartphone.android.banking.bb de.fiducia.smartphone.android.banking.psd de.fiducia.smartphone.android.banking.vr de.fiducia.smartphone.android.securego.vr de.ing_diba.kontostand de.postbank.finanzassistent de.sdvrz.ihb.mobile.app de.sdvrz.ihb.mobile.secureapp.netbank.produktion de.sdvrz.ihb.mobile.secureapp.sparda.produktion enbd.mobilebanking enbd.mobilebanking.ksamobile enbd.mobilebanking.smartbusiness es.bancopopular.nbmpopular es.bancopopular.nbmpopulartablet es.bancosantander.apps es.bancosantander.empresas es.bancosantander.wallet es.bmn.bmnapp2 es.bmn.cajagranadaapp2 es.bmn.cajamurciaapp2 es.bmn.sanostraapp2 es.caixagalicia.activamovil es.caixageral.caixageralapp es.ccm.ccmapp es.cm.android es.cm.android.tablet es.connectis.mobile.alrajhi es.evobanco.bancamovil es.lacaixa.hceicon2 es.lacaixa.mobile.android.newwapicon es.liberbank.cajasturapp es.redsys.walletmb.app.kutxa.pro es.redsys.walletmb.app.laboralkutxa.pro es.santander.money es.univia.unicajamovil eu.eleader.mobilebanking.abk eu.eleader.mobilebanking.bre eu.eleader.mobilebanking.nbk eu.eleader.mobilebanking.pekao eu.eleader.mobilebanking.pekao.firm eu.eleader.mobilebanking.raiffeisen eu.inmite.prj.kb.mobilbank finansbank.enpara fr.banquepopulaire.cyberplus fr.banquepopulaire.cyberplus.pro fr.banquepopulaire.cyberplustablet fr.bred.fr fr.creditagricole.androidapp fr.creditagricole.macarteca fr.lcl.android.customerarea fr.lcl.android.entreprise ftb.ibank.android gr.winbank.mobile hr.asseco.android.jimba.mUCI.cz hr.asseco.android.jimba.mUCI.cz.tablet hr.asseco.android.mtoken.credem.credemprod hr.asseco.android.mtoken.pekao it.bcc.iccrea.mycartabcc it.bnl.androidTablet it.bnl.apps.banking it.bpm.bpmandroid it.bpm.ptbandroid it.carige it.cividale.bpconline it.copergmps.rt.pf.android.sp.bmps it.copergmps.rt.pf.android.tab.ui.bmps it.creval.bancaperta it.elfisystems.ncbc.droid.tablet it.elfisystems.ncbc.mobile it.gruppobper.ams.android.bper it.ingdirect.app it.nogood.container it.popso.SCRIGNOapp it.relaxbanking it.reply.up.mobile.android it.secservizi.mobile.atime it.secservizi.mobile.atime.bpaa it.secservizi.mobile.atime.bpvi it.ubi.digitalcode it.ubiss.mpay it.volksbank.android mbanking.NBG mobi.societegenerale.mobile.lappli mobi.societegenerale.mobile.lapplipro mobile.alphabank.myAlphaWallet_android mobile.santander.de net.atos.alrajhi.mobilekw net.bnpparibas.mescomptes net.inverline.bancosabadell.officelocator.android nl.asnbank.asnbankieren nl.rabomobiel nl.regiobank.regiobankieren nl.snsbank.snsbankieren nl.snsbank.snshelp nz.co.amp.myportfolio.android nz.co.anz.android.mobilebanking nz.co.asb.asbmobile nz.co.asb.mobilebusiness nz.co.bnz.droidbanking nz.co.bnz.droidbusinessbanking nz.co.cooperativebank nz.co.kiwibank.mobile nz.co.westpac org.banelco org.banelco.ibay org.banelco.qlms org.banelco.rbts org.banelco.sdmr org.banking.bom.businessconnect org.banking.bsa.businessconnect org.banking.stg.businessconnect org.banksa.bank org.bom.bank org.microemu.android.model.common.VTUserApplicationLIN org.microemu.android.model.common.VTUserApplicationLIN org.stgeorge.bank org.westpac.bank org.westpac.col pl.aliorbank.kantorwalutowy pl.bzwbk.bzwbk24 pl.bzwbk.ibiznes24 pl.bzwbk.mobile.tab.bzwbk24 pl.com.suntech.mobileconnect pl.eurobank pl.ing.ingmobile pl.ipko.mobile pl.mbank pl.millennium.corpApp pl.pkobp.iko posteitaliane.posteapp.appbpol pt.BancoPopular.android.app pt.bancobest.android.mobilebanking pt.bancobpi.mobile.autorizacoesempresas pt.bancobpi.mobile.fiabilizacao pt.bes.bestablet pt.cgd.caixadirecta pt.cgd.caixadirectaempresas pt.novobanco.nbapp pt.santandertotta.mobileparticulares pt.sibs.android.mbway riyad.bankingapp.android rm.beleggen tr.com.sekerbilisim.mbank tsb.mobilebanking uk.co.bankofscotland.businessbank uk.co.metrobankonline.personal.mobile uk.co.northernbank.android.tribank uk.co.santander.businessUK.bb uk.co.santander.santanderUK uk.co.tsb.mobilebank wit.android.bcpBankingApp.activoBank wit.android.bcpBankingApp.millennium wit.android.bcpBankingApp.millenniumPL www.ingdirect.nativeframe com.android.vendin